Cybersecurity threats have become increasingly intricate and have emerged as a significant risk to individuals and organizations. Therefore, it is essential to leverage advanced cybersecurity software solutions that provide multiple layers of defense to protect against potential threats.
Learning cybersecurity and gaining a comprehensive understanding of cyber-attack types empowers professionals to implement robust cybersecurity solutions that ensure the confidentiality, integrity, and availability of digital data.
This article aims to provide insights into the top 7 cybersecurity software solutions, including their capabilities, advantages, and pricing. Software solutions effectively prevent many notorious cyber attacks, including zero-day attacks, and offer cybersecurity best practices to reduce the threat landscape.

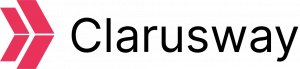
What are the Top 7 Cybersecurity Software?
There are various software options available that provide effective cybersecurity solutions to protect digital presence. Here are the top 7 cybersecurity software programs:
- CrowdStrike Falcon
- Splunk Enterprise Security
- Wireshark
- Bitdefender Total Security
- Fortinet Fortigate Firewall
- Snort
- Proofpoint Essentials Email Security
CrowdStrike Falcon
The CrowdStrike Falcon is a security solution that ensures endpoint protection. The Falcon identifies and prevents cyber threats in real-time, giving security teams early warning and the ability to respond quickly. The CrowdStrike is easy to use and has been named the leader in endpoint protection by Forrester’s Endpoint Security report.
Advantages:
The Falcon is a cloud-based software that swiftly detects and responds to cyber threats. It provides visibility into endpoints, an extensive threat database, and behavioral approaches.
Category:
Cloud-based endpoint protection.
Pricing:
There are 3 options: Falcon Pro, Enterprise, and Elite, starting from $499.95 annually. The minimum purchase is 5 devices, and it is limited to a maximum of 100 devices for each bundle.
Splunk Enterprise Security
Splunk is a powerful tool that helps to monitor, detect, and investigate threats quickly and accurately. It uses machine learning to detect threats and provides complete visibility, making investigations more efficient. Splunk is the best SIEM solution, according to the 2022 Gartner Magic Quadrant for SIEM report, for a total of 9 years in a row.
Advantages:
Splunk has accelerated threat detection, compatibility, and flexibility that unify security operations. Automating security workflows simplifies the process and reduces the manual work required by analysts, leading to faster response times.
Category:
Security Information and Event Management (SIEM).
Pricing:
Splunk offers 3 pricing models: ingest, workload, and entity pricing. The pricing policy is customized based on the specific solution required.
Wireshark
Wireshark is a free, open-source packet sniffing tool to monitor and analyze network traffic. It captures real-time unencrypted traffic through a network interface.
Advantages:
Wireshark is a free and user-friendly software that helps cybersecurity experts analyze networks in real-time or offline across various operating systems. Wireshark also has educational value in explaining how networks work.
Category:
Network protocol analyzer.
Pricing:
Free
Bitdefender Total Security
Bitdefender Total Security enables cyber resilience and enhances cybersecurity compliance by providing firewall, email security, and ransomware protection. Multi-layer protection offers robust protection for individuals and businesses.
Forbes says it is the “best overall” software for cost-benefit analysis.
Advantages:
Bitdefender safeguards against malware with the lowest impact on performance. Anti-phishing protection and innovative techniques against zero-day attacks make Bitdefender a top-notch anti-malware software.
Category:
Anti-malware software.
Pricing:
Bitdefender offers two pricing models: one for home users and one for businesses. For home users, the annual price starts at $59.99. For enterprises, customers will need to request a quote.
Fortinet Fortigate Firewall
The Fortinet Fortigate Next-generation firewall (NGFW) helps manage network traffic and protect against cyber threats. The Fortigate NGFW provides malware detection, intrusion prevention, deep-packet inspection, and application control to ensure a strong security posture. Fortigate is the most widely used network firewall, according to the Gartner Peer Insights Customers’ Choice.
Advantages:
FortiGate is easy to use with both a GUI and a CLI. It offers complete protection for digital assets in remote locations or the cloud. FortiGate also provides multiple layers of security with macro- and micro-segmentation qualifications. Fortinet provides the necessary training to support its customers.
Category:
Next-generation Firewall (NGFW).
Pricing:
Various factors, such as the size of the business, integration of security systems, and any agreements in place, determine the associated costs. Customers should request a quote.
Snort
Snort is an IDS/IPS software within the Cisco brand that monitors real-time network traffic and alerts users to emerging threats. Snort has 3 primary functions: packet sniffer, packet logger, and network intrusion prevention system (NIPS).
Advantages:
Snort is an open-source application that offers a free version. It’s easy to use, highly customizable, and receives community-driven updates. It can be installed and run in any network environment.
Category:
Network intrusion prevention system.
Pricing:
Snort offers a free version, but the paid option provides more advanced features. Snort has two subscription models, one for personal use and the other for businesses. The yearly subscription starts at $29.99 for individuals; custom pricing is available for companies.
Proofpoint Essentials Email Security
Proofpoint Essentials Email Security is a cloud-based email security solution offered by Proofpoint. Email security is critical as most cyber-attacks happen through email scams and social engineering tactics, according to CISCO’s Cybersecurity Threat Trends report. To protect against these advanced threats, Proofpoint Essentials is a trusted email security solution that can detect harmful URLs or attachments in emails.
Advantages:
Proofpoint Essentials provides extra features like social media protection, email encryption, and attachment sandboxing. It can be implemented through an on-premise or cloud-based solution, making it an easy and cost-effective way to meet cybersecurity requirements.
Category:
Email security and protection.
Pricing:
Proofpoint Essentials offers affordable pricing plans for both beginners and professionals, starting at $3.03 per month for essential beginner features.
Comparison of Top 7 CyberSecurity Software
Here is the comparison of the top 7 cybersecurity software providers;
| Category | Free Trial | Price | |
| CrowdStrike Falcon | Cloud-based endpoint protection | 15 days | Paid |
| Splunk Enterprise Security | Security Information and Event Management (SIEM) | 60 days | Paid |
| Wireshark | Network protocol analyzer. | Free | Free |
| Bitdefender Total Security | Anti-malware software | 30 days | Paid |
| Fortinet Fortigate Firewall | Next-generation Firewall (NGFW) | 14 days | Paid |
| Snort | Network intrusion prevention system (NIPS) | Free | Free/paid |
| Proofpoint Essentials Email Security | Email security and protection | 30 days | Paid |
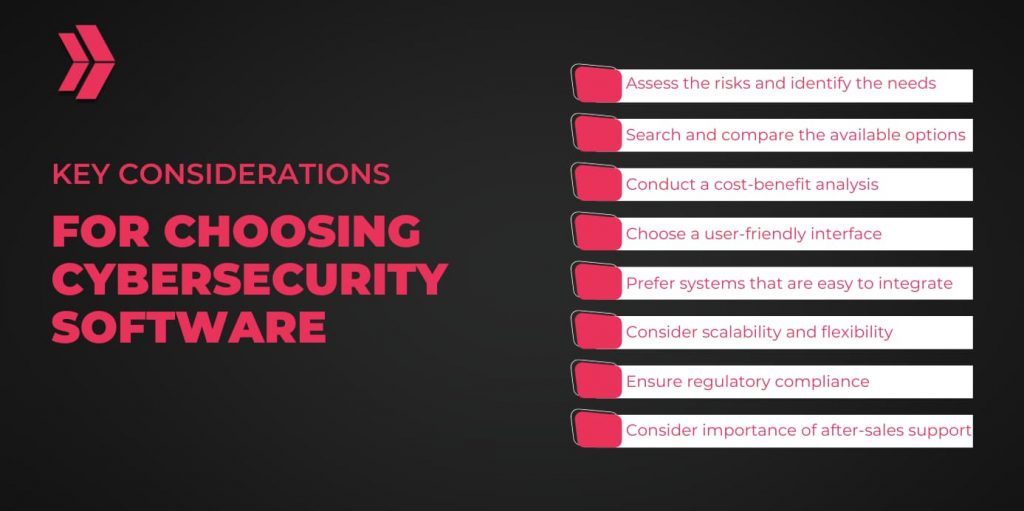
What are the Key Considerations When Choosing Cybersecurity Software?
Choosing the best cybersecurity software is critical for individuals and organizations to safeguard digital assets. Here are the some key considerations:
- Assess the risks and identify the needs
- Search and compare the available options
- Conduct a cost-benefit analysis
- Choose a user-friendly interface
- Prefer systems that are easy to integrate
- Consider scalability and flexibility
- Ensure regulatory compliance
- Consider the importance of after-sales support
How Can Cybersecurity Software Protect from Evolving Threats?
The best cybersecurity software can enhance the overall security posture and protect from evolving threats in 5 main ways by providing:
- Data protection by solid encryption
- Proper authentication and authorization procedures
- Real-time monitoring, incident response, and recovery
- Cyber threat intelligence to preempt and prevent threats
- Regular updates and patch management

What Are Zero-Day Vulnerabilities, and How Does Cybersecurity Software Address Them?
A zero-day vulnerability is a security flaw that is unknown to related parties. However, a zero-day attack occurs when attackers exploit zero-day vulnerabilities to cause harm without detection. Here are 7 significant ways that cybersecurity software can help prevent and manage zero-day attacks:
- Patch and update systems regularly
- Prioritize risk management
- Implement continuous monitoring
- Devise a comprehensive incident response plan
- Conduct periodic vulnerability scanning
- Leverage threat intelligence and information-sharing platforms
- Consider and plan for bug bounty programs.
Why is Cybersecurity Software Vital to Staying Ahead of Cyber Attacks?
Cybersecurity software is vital for staying ahead of attacks by providing real-time monitoring, threat intelligence, and proactive measures. It establishes and maintains a robust defense mechanism against evolving cyber attack types, ensuring the safety of valuable assets.
What Are The Best Practices For Keeping Up With Cybersecurity Trends and Developments?
Here are some cybersecurity best practices for staying up-to-date on cybersecurity trends and advancements:
- Utilize online resources to stay up-to-date
- Read reliable reports and newsletters
- Follow respected experts on social media
- Participate to relevant events and conferences
- Collaborate and share ideas with peers
What Is The Role of Cybersecurity Engineers in Protecting Your Data Against Emerging Threats?
An engineer plays a pivotal role in implementing and designing cybersecurity measures to protect networks and systems. A cybersecurity engineer also detects and addresses potential security threats through vulnerability scans, thereby minimizing the attack surface and reducing the risk of cyber attacks.
A cybersecurity software engineer troubleshoots emerging problems, oversees digital infrastructure, and supervises technical issues while implementing system-hardening measures to improve security posture.
In conclusion, the constantly evolving nature of cyber threats demands robust software solutions to counter emerging and complex threats. The top 7 advanced cybersecurity software solutions tackle various security challenges, from vulnerability management and encryption to threat detection and prevention. Utilizing software solutions is critical to bolstering digital defenses, identifying unforeseen vulnerabilities, and preventing cyber attacks. As a result, cybersecurity software improves overall security posture.