Learning cybersecurity is essential to safeguarding individuals and organizations against cyber threats that can significantly threaten sensitive data, cause system disruptions, and lead to substantial financial and reputational damage.
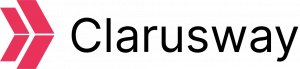
Cyber attacks worldwide rose by 38% in 2022 compared to the previous year, according to the 2023 Cyber Security Report published by Check Point. IT professionals must be mindful of various cyber threats, including the four most common types of cyber attacks: social engineering, malware, code injection, and DDoS attacks.

The article delves into different types of cyber attacks, their implications, and measures to prevent and respond to them.
What is a Cyber Attack, and How Does it Relate to Cybersecurity?
A cyber attack is a malicious act aimed at gathering, disrupting, revealing, or stealing crucial digital assets. On the other hand, cybersecurity ensures the safety and security of systems, networks, and data from potential cyber threats.
In the digital landscape, cyber attacks and cyber security are closely intertwined and intricately linked concepts that focus on unauthorized access or breaches across multiple areas, including application, information, network, and cloud security.
What Are the 4 Types of Cyber Attacks?
Cyber attacks encompass a range of methods employed by threat actors to breach computer systems, networks, and devices. Generally, cyber criminals use the top 4 common types of cyber-attacks mentioned below:
- Social Engineering Attacks
- Malware Attacks
- Code Injection Attacks
- DDoS Attacks (Denial of Services)
Now, we can provide comprehensive explanations for each of these attacks.
What is a Social Engineering Attack?
A social engineering attack is a malicious activity that uses psychological manipulation techniques to trick victims into compromising sensitive information. As articulated by CompTIA, social engineering is responsible for an overwhelming 98% of successful cybercrime.
Phishing attacks are the most common vector for social engineering attacks. Undoubtedly, the human factor remains the most vulnerable aspect of cybersecurity.
While cybercriminals employ various social engineering tactics, 7 the most commonly used attack methods include phishing, spear phishing, whaling, smishing, vishing, pretexting, and pharming.
| Phishing | Tricking victims into exposing personal data. |
| Spear Phishing | Targeting specific people with detailed information. |
| Whaling | Targeting high-value executives for scams. |
| Smishing | Using SMS messages for phishing. |
| Vishing | Using voice calls for phishing. |
| Pretexting | Fabricating scenarios to impersonate trusted resources. |
| Pharming | Redirecting internet traffic to a fake website to obtain credentials. |
What is a Malware Attack?
A malware attack is an intrusive action designed to steal, damage, or exploit servers, networks, or end devices. The world experienced 5.5 billion malware attacks in 2022, according to Statista. Malware, also known as malicious software, is a broad term encompassing various types of cyber attacks.
Ransomware attacks are one of the most prevalent forms of malware attacks. Over a million ransomware attacks occur daily, costing billions of dollars annually.
Here, we will explore the most common 7 malware attack types with the list below:
| Ransomware | Encrypts data and demands a ransom to provide a decryption key. Generally, cryptocurrency is the preferred payment method. |
| Virus | Modifies or deletes files by attaching malicious executable codes. It needs a host for activation and cannot be controlled remotely. |
| Worms | Replicate and propagate itself to consume system resources. Worms can spread to other computers on networks and be controlled remotely. |
| Trojan | Infects the target with malicious codes while masquerading as a legitimate program. When infiltrated, it can carry out harmful operations. |
| Keylogger | Monitors and records keystrokes as typed in. This surveillance software is used for keystroke logging. |
| Rootkit | Controls the target without the user’s knowledge or permission. A rootkit allows remote access and can hide its presence and actions. |
| Fileless malware | Utilizes existing protocols, applications, and software to carry out harmful actions and obtain authority. It is hard to detect and does not require an executable code or file on the target. |
Code Injection Attacks
Code injection attacks insert harmful code into a vulnerable network or computer to manipulate its behavior. Attackers send a request containing malicious injection code to their target. The primary goal of code injection attacks is to steal, alter, or delete information from the intended target.
Code injection attacks can have harmful consequences, including information disclosure, authentication bypassing, data loss, and privilege escalation.
Cross-Site Scripting (XSS) and SQL Injection are among the most common types of attacks. According to Purplesec, SQL injection attacks make up almost 26% of cyber attacks targeting small businesses.
Cybercriminals employ various types of code injection attacks. However, in this text, we will focus on the top 4 types as follows:
| SQL Injection | Uses SQL syntax to inject harmful commands that can either modify or read a database or even manipulate the intended meaning of the initial query. |
| LDAP Injection | Compromises the authentication process when input validation is absent or weak. Permissions, roles, and users can be modified or erased. |
| Cross-Site Scripting (XSS) | Injects harmful executable scripts into the code of a reliable website or application that accepts user input. |
| Command Injection | Executes commands in the target operating system using a system shell. It differs from code injection attacks by working without injecting malicious code. |
What is a DDoS Attack?
A denial-of-service (DDoS) attack is a hostile act aimed at overwhelming and disrupting a target with a large volume of internet traffic. The DDoS attacks increased by 273 compared to the previous year, according to the DDoS Attack Landscape Report published by NSFocus in 2022.
There are some differences between DoS and DDoS. A DoS attack floods the victim from a single source, while a DDoS attack uses multiple sources from different locations. Similarly, a DoS attack is slower and easier to mitigate compared to DDoS attacks.
Attackers often utilize 3 main DDoS techniques as follows:
| Application Layer Attack | Focuses on the application itself and takes advantage of weaknesses in layer 7 of the OSI model. Application Layer attacks are challenging to identify and protect against. |
| Protocol Attack | Disrupts the target by over-consuming resources. It generally exploits the vulnerabilities of the OSI model in Layer 3 and Layer 4. |
| Volumetric Attack | Overwhelms the network bandwidth by generating massive traffic volumes. This is the most common attack technique used by offenders. |
How to Prevent Cyber Attacks?
To prevent cyber attacks, the most common solutions are awareness training, system hardening, and implementing best practices. However, the four types of attacks discussed in this article require unique and tailored solutions for each style.
IT professionals can apply numerous measures to prevent malware attacks, including employee training, using security software, implementing multi-factor authentication and strong password practices, restricting privileges, and constantly monitoring cyber intrusions.
Social engineering attacks can be prevented through various methods, such as awareness training, securing your digital footprint, implementing multi-factor authentication, and regularly updating security patches.
The most effective methods to prevent code injection attacks are whitelisting and input validation. Additionally, specific tools provide web vulnerability scanning.
Some ways to mitigate DDoS attacks include having a robust response plan, network segmentation, rate limiting, blackhole routing, and using a Web Application Firewall (WAF).
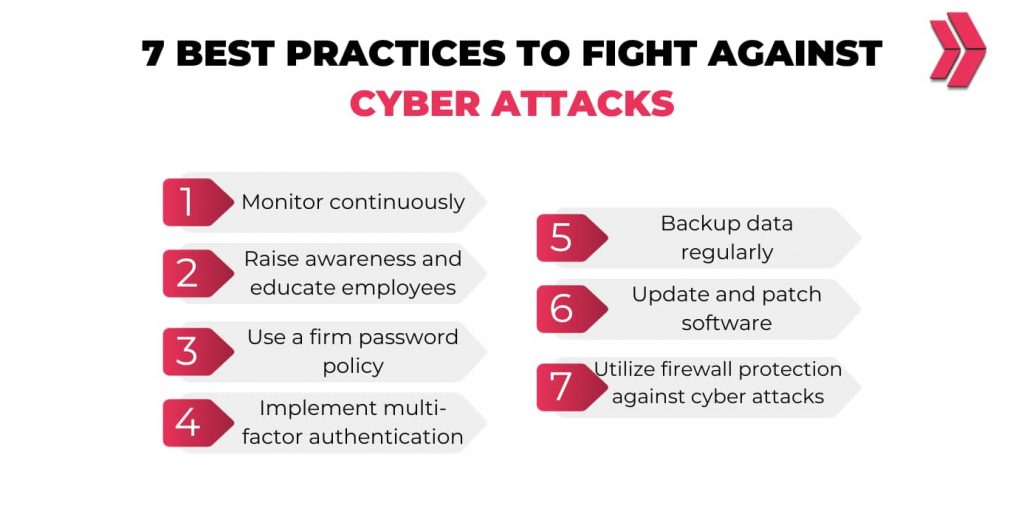
What Are the Best Practices in Cyber Security for Preventing and Responding to Cyber Attacks?
To effectively prevent and respond to cyber-attacks, it’s essential to implement a multi-layered approach to cyber security practices. Here, we will mention the 7 best practices to fight against cyber attacks:
- Monitor continuously.
- Raise awareness and educate employees.
- Use a firm password policy.
- Implement multi-factor authentication
- Backup data regularly.
- Update and patch software.
- Utilize firewall protection against cyber attacks.
What is the Role of Cybersecurity Professionals in Preventing and Responding to Cyber Attacks?
Cybersecurity professionals play a significant role in safeguarding against and responding to cyber-attacks. Their responsibilities include ensuring the security of IT systems, monitoring and detecting security breaches, conducting audits and implementing security measures for cyber attack protection.
There are various roles available in preventing cyber attacks. However, a cybersecurity analyst is the first line of defense to secure networks, systems, and data against various cyber threats.
How Often Do Cyber Attacks Occur?
On average, cyberattacks occur every 39 seconds, costing billions of dollars.
What Happens During a Cyber Attack?
Criminals constantly launch cyber attacks, and robust security measures do not always prevent them. If these attacks are successful, they result in financial losses and harm to reputation and intellectual property due to a data breach.